![]()
BackBox Linux 4.4 is a great Linux distro for IT and other techies who want to do their own penetration tests and security assessments.
The latest version, released this month, is an Ubuntu 14.04.3-based distribution that is speedy and simple to use. It is a fully functional Linux distro that comes well stocked with standard software. It runs a desktop environment based on the Xfce window manager, which makes it standard and uncomplicated to use.
BackBox has its own software repositories. If its toolshed ended there, it would be a solid yet typical old-style Linux operating environment. The developers, however, added a state-of-the-art workroom with the latest stable versions containing some of the most often used and best-known ethical hacking tools.
However, BackBox is not unique in its mission to provide a tailored environment for assessing security issues. It takes a different approach in its intended uses thanCAINE Linux, a professional-grade digital forensic OS. CAINE stands for Computer Aided INvestigative Environment.
BackBox, like CAINE, helps you make your personal computing activities more hardened or hidden. BackBox does a lot more than merely masking your identity while navigating the Internet. For just that, you might want to investigateTails Linux. TAILS, otherwise known as The Amnesic Incognito Live System, focuses on preserving privacy and anonymity online.
BackBox’s developers built into this release some new features that provide a collection of security tools to harden files and some OS components easily. These tools are not part of the typical XFCE desktop or standard distro repositories.
Two Faces of Security
BackBox puts a focus on Web application analysis, network analysis, stress tests and sniffing. Its usefulness is extended with software packages for vulnerability assessment, computer forensic analysis and exploitation.
CAINE, on the other hand, supports the digital investigator during the four phases of computer digital investigations: seizure, acquisition, analysis and reporting. Some of the tools are similar, but the intended use is much different.
BackBox targets two key goals: delivering high performance and operating with minimal resource consumption. Those two factors make it an ideal partner on older hardware.
Neither distro is specially hardened to make it more secure than other Linux OS options. BackBox excels in the hands of users looking for secure security research.
BackBox offers an effective specialty mission centered on security. All three security-minded distros are based on Ubuntu Linux.
Look and Feel
BackBox has a classic Linux OS appearance. Its Xfce desktop environment works as you expect.
For example, the traditional panel bar sits at the top of the screen. You can configure it your way, setting preferences and adding/removing panel applets at will.
The workplace switcher applet is not preconfigured, but it is easy to add with a right-click on the panel bar. The main menu button is located at the far left. Right-click anywhere on the desktop to open a secondary menu.
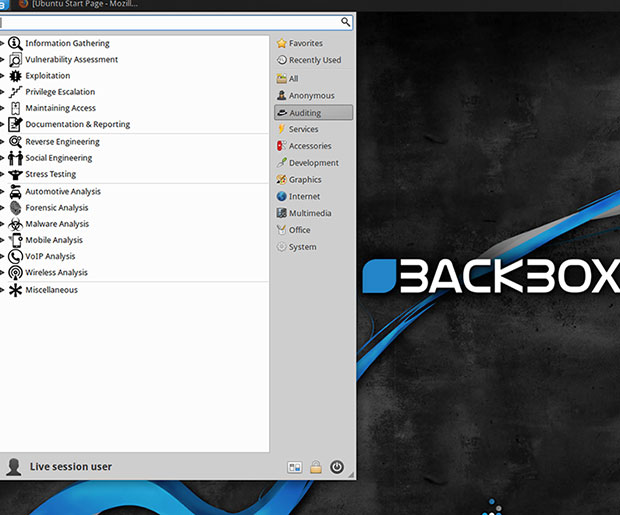
Very little in the BackBox theme is distracting. It lacks color and flash. The background is shades of black and gray. A wavy two-tone blue swirl runs from the lower left to the upper right corners of the screen.
Mellow Menu
The menu system maintains the no-distractions theme. It is the standard Xfce design with two columns in black and white.

The right column holds the categories, while the larger left column displays the applications for the selected category. A search window resides at the top of the menu box. Icons for All System Settings and Power Off are in the lower right corner.
One of the handiest features of the Xfce desktop is the right-click menu access. This menu is a single column with cascading displays where needed for selection options.
Under the Hood
The BackBox community makes three releases per year to keep the distro up to date with the latest developments in security. BackBox 4.4 comes also with Kernel 3.19 and is built around Ubuntu 14.04.3.
This current release includes some nice special touches. For instance, the Thunar file manager has a custom actions feature that lets you put frequently used security commands in context menus. These include actions such as open folder as root, open terminal as root in current folder, clean metadata from files, encrypt with GPG, and secure delete.
New special features include the ability to wipe contents in RAM at shutdown or reboot and an improved Anonymous Mode. This release also has updated hacking tools such as apktool, armitage, BeEF Project, can-utils, dex2jar, fimap, JD-GUI, metasploit-framework, OpenVAS, setoolkit, sqlmap, Tor, Weevely, WPScan and zaproxy.
System requirements are fairly flexible and allow most legacy hardware to run without issues. You need a 32-bit or 64-bit processor with at least 512 MB of system memory, or RAM. Installation requires 6 GB of disk space. The graphics card must be capable of 800600 resolution. A DVD-ROM drive or USB port also is needed.
Legacy Linux Lingers
BackBox comes with many of the everyday computing applications preinstalled. The default browser is Firefox, but the Tor anonymous browser also is included.
I was pleased to find my favorite multipurpose IDE text editor, Geany, preinstalled. Other standard accessories include the Mousepad text editor, Notes and Zim Desktop Wiki.
Other standard Linux must-have preinstalled applications make BackBox a fully functional and very useful operating system out of the box. For instance, it includes Xburn for CD/DVD writing, GIMP Image Editor, recordMyDesktop, several media players and the LibreOffice suite.
Specialty Security Software
The big differentiator for BackBox over other distro choices is the security-sniffing applications assembled in the Anonymous and Auditing menu categories. This is where the quest for penetration tests and security assessments really pays off.
For instance, clicking on the Anonymous Start option runs a series of commands in a terminal window asking for your preferences for the computing session. In addition to automatically killing services to prevent leaks, you can choose to change the MAC address and the local hostname, and transparently route traffic through Tor.
The security auditing options are extensive. They provide the ability to check your local network’s integrity as well as better lock down your computing session.
The Auditing menu has 16 categories, each with numerous subcategories. Most of the options run commands and display results within a terminal window. Other titles, such as MagicTree, have user interfaces to set the conditions for running various penetration tests and viewing the results.
Bottom Line
You can use BackBox as your main Linux distro and do nothing more involved that run its security envelop to harden your immediate computing environment and surf the Web with anonymity.
You can use BackBox more productively to dig deep into your network to sniff out security risks and lock down your connectivity and data. BackBox’s security tools are professional class.
Unless you are schooled in using them, you will have to spend time familiarizing yourself with each of the tools. The only real weakness in this distro is the lack of centralized documentation for using the security software and terminal commands for the auditing processes. You are on your own.
Most of the security applications run well in live session, so you can sniff around for security problems in your local network and wireless connectivity without installing BackBox to any particular computer’s hard drive.
Want to Suggest a Review?
Is there a Linux software application or distro you’d like to suggest for review? Something you love or would like to get to know?
Please email your ideas to me, and I’ll consider them for a future Linux Picks and Pans column.
And use the Talkback feature below to add your comments!






















































Hey interesting review, I was curious about the lack of documentation on software. What’s wrong with the man pages? That’s what they’re there for or am I not understanding what you meant.